|
by James Corbett
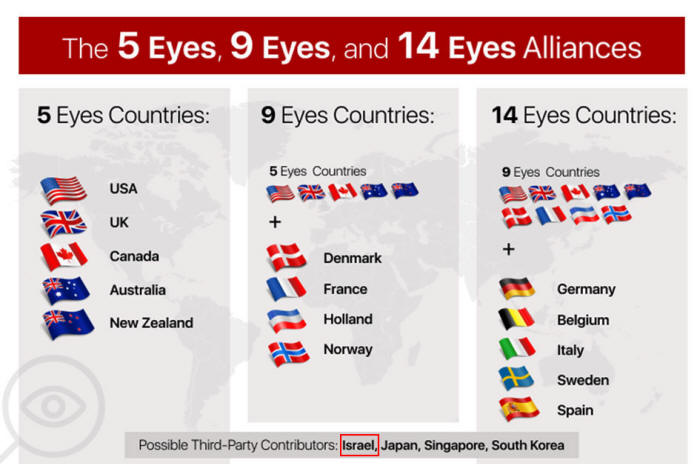
And, despite what the MSM says, he wasn't making Kompromat for his KGB komrades so much as he was wheeling and dealing for his friends, the Israelis.
In addition to the many, many ties to Israel I listed in my 10 Things I Learned from the Epstein Files editorial, more and more data continues to emerge showing how Epstein worked with his pal (and ex-Israeli Prime Minister) Ehud Barak to secure contracts and achieve diplomatic objectives for Israel.
This data includes information on how Epstein:
Heck, the Israeli government even installed and maintained the security system at the Manhattan apartment Epstein frequently lent out to Barak.
Yes, whatever else Epstein may have been doing, it seems he was working diligently behind the scenes as an agent of influence to promote Israeli interests around the world.
But Epstein is dead, as you may have heard.
So,
As it turns out, we can catch glimpses of the answer to that question in the Epstein files, too...
THE CARBYNE CREW
Last November, the San Francisco Standard published "Inside the extended courtship linking Jeffrey Epstein, Peter Thiel, and Israeli officials."
The article details how Handala (an "Iran-linked hacking group") obtained emails from Israeli officials that show that Epstein was once again the lubricant greasing the skids for the Israeli deep state in their attempt to woo the Silicon Valley broligarchs.
First, Epstein courted Thiel:
Then, he introduced Thiel to Barak:
So, what became of this relationship?
As Drop Site News reported last month,
Originally called "Reporty," Carbyne didn't just receive funding from Epstein.
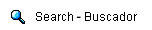
The company wasn't just chaired by Barak. It didn't simply boast Sultan Ahmed bin "loved the torture video" Sulayem among its investors.
It also just happened to be founded by Amir Elichia, a veteran of Israel's cyberspook signals intelligence service, Unit 8200...
In other words,
None of this is news to those who followed Whitney Webb's reporting on the subject back in 2019, of course.
But the recently released Epstein files contain more information on these connections, including the actual correspondence between Epstein, Barak, Thiel, Sulayem and the other people involved in this venture as well as the actual documents they were examining.
The story of Carbyne - an Israeli intelligence-founded and Israeli-backed company seeking to worm itself into the emergency response systems of countries around the world, including the US - is important in and of itself.
Those interested in exploring the subject really owe it to themselves to read Webb's original reporting on the topic from 2019.
But the Carbyne saga is not just interesting in and of itself.
Firstly, it provides a window into the story of Unit 8200, Israel's infamous cyberspy team...
THE 8200 GANG
As noted above, Carbyne's founder and CEO was Amir Elichai.
The company's "About Us" page helpfully explains the Eureka moment that prompted Elichai to create the company:
What Carbyne's "About Us" page unhelpfully leaves out, however, is Elichai's background.
This was not some random mugging victim (assuming such a mugging ever actually took place).
Rather, as Adam Bensaid reported for TRT World back in 2019, Elichai was,
And he wasn't the only "ex"-Israeli intelligence official on the company's board.
...and, as Bensaid also reports, the company's first director had his own link to Israeli intelligence.
So, what is Unit 8200, exactly?
As I explained in "Beyond Pegasus - The Bigger Picture of Israeli Cyber Spying," my 2021 editorial on Israel's military-grade "Pegasus" spyware:
And what acts of cyber espionage have Unit 8200 been involved in, exactly? How about acts such as:
There are doubtless many other examples of perfidy and war crimes perpetrated or enabled by Unit 8200, but, given that it is an intelligence agency, such actions are still heavily classified.
Arguably more important than the operations Unit 8200 members conduct while still active members of the organization, however, are the companies they form after leaving the spy unit.
As one 8200 veteran, Avishai Abrahami, told Forbes in 2016, the prevalence of "ex"-8200 members in Silicon Valley is by now impossible to ignore:
Again, as I reported in "Beyond Pegasus":
The companies formed by these "former" 8200 operatives include not just Carbyne, but. The fact that so many high-tech Israeli companies at the heart of America (and the world's) emergency responses, communication infrastructure, payment systems and digital forensic tools have been founded by military-trained Israeli cyber intelligence officers should tell us something.
Namely,
Yes, as the Epstein/Thiel/Barak/Elichai nexus found in the Epstein files themselves informs us, the growing importance of the Unit 8200 gang in the heart of the global cybersecurity industry reflects a fundamental change that has taken place in intelligence in recent decades.
In short, the spooks and spies are moving away from the old-school flesh-and-blood-style sexpot honeytraps that characterized the Epstein era of espionage and moving toward the Palantir-esque panopticon backdoor surveillance that characterizes the post-Epstein era of espionage.
FROM HONEYTRAPS TO PANOPTICON
Anyone who's been paying even cursory attention to the workings of the kakistocracy over the past century will know that good old-fashioned blackmail has worked to ensure the deep state's control over their puppets in the surface state for decades if not centuries (if not millennia).
And no blackmail works as well as sexual blackmail...!
We know, for instance, that J. Edgar Hoover had blackmail on every political player of consequence in Washington during his nearly half-century tenure as director of the FBI, including (it is alleged) the Kennedy brothers.
And readers of Whitney Webb's One Nation Under Blackmail will know about the many, many ways that those in and around power in American politics have been steered into compromising positions for the purpose of being put under the thumb of various criminal elements.
Of course, these are just a few of the examples of sexual blackmail that we know about and have documentary evidence of. There are many, many more examples about which we have only the outline of the story.
But throughout the long, sordid history of blackmail, there has always been the need for would-be blackmailers to find, entice, record and recruit the target in question.
Hitherto, this has required would-be blackmailers to engage in elaborate setups, including bringing targets to facilities that have been bugged with recording devices.
As successful as such tactics have historically proven to be, they are undoubtedly difficult, cumbersome and unreliable.
A target with anything approaching a degree of discretion or basic training in espionage would likely recognize that they were being led into a honeytrap long before the trap could be sprung.
As the Epstein files also demonstrate, as often as Epstein and Maxwell were able to lure wealthy and powerful figures into their orbit and entice them to the island or the ranch or the Manhattan apartment, they were just as often unsuccessful in digging their talons into their target.
There were many would-be victims of Epstein's blackmail operation who sensed that something was off and rejected his or Ghislaine's advances.
But in our current digital dystopia, such tactics aren't necessary.
At this point, everyone is carrying a tracking and recording device with them 24/7.
And, wouldn't you know it, the development of just such spyware technology is exactly what Israeli intelligence has been working on feverishly.
Of course, there would be one obvious way to diminish the influence of these Israeli cyber spies:
In the wake of the Pegasus spyware scandal in 2021, there was a moment where it looked like the EU was actually going to do the bare minimum to clear this incredibly low threshold of "action" on the spyware subject.
After a European Parliament committee examining the use of spyware in Europe issued a blistering report,
Even the EU's cheerleaders had to admit that the parliament's totally ineffectual response means that it will continue to be business as usual for the (mostly Israeli) spyware industry.
And - whodathunkit? - those detractors have been proven right.
Just last summer, the EU was struck with yet another spyware scandal.
So, how about Uncle Sam?
In a move that will surprise precisely no one, the US government has now doubled down on its reliance on Israeli-produced spyware.
In fact, as Reuters reported last month, the Trump administration is actively working to remove sanctions on Israeli spyware-linked executives.
But don't worry, Americans...
In an article last year on how "America now leads the world in surveillanceware investment," The Register reported on one such Israeli surveillanceware company, Saito Tech Ltd, which was sanctioned by the US Commerce Department in 2021,
After the sanction, US investors didn't shy away from the sanctioned company. Instead, they bought it out.
Yes, spyware is big business, and every government wants a piece of the action...
It just so happens that Israeli intelligence has just about cornered the market.
Given all of this information, it's no surprise that signs of the changeover in intelligence methods from real-world honeytraps to cyber surveillance are to be found in the Epstein files.
Perhaps the only real surprise here is that it took so long for the powers-that-shouldn't-be to realize Epstein was becoming more of a liability than an asset and to take measures to tie up that loose end.
|