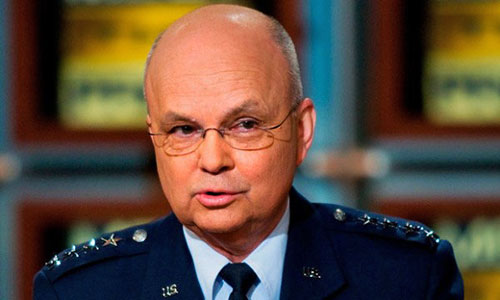
Michael Hayden, former director of the
National Security Agency (NSA)
and the Central Intelligence Agency (CIA),
spoke at George Mason University’s School of Public Policy (SPP)
about "The
Future of Surveillance in a Post-Snowden World."
Hayden is
concerned about the leaks
Edward Snowden has made and the changes to
surveillance they have caused.
The former CIA head said:
"I believe that Snowden has badly shaped
this debate and, in the course of this acceleration, created a media
frenzy that is largely focused on headline-grabbing sensationalism
rather than speaking to the hard facts."
Snowden has,
"revealed far more sensitive intelligence"; compromising
the secret world of government spying with public knowledge of "sources
and methods" the NSA uses to "conduct its electronic eavesdropping."
Hayden asserts that,
"well over 90 percent of what Snowden has
revealed has had nothing to do with Americans’ communications.
Rather,
Snowden has compromised how the US goes about collecting the
communications of non-U.S. persons who are, in fact, legitimate
intelligence targets; these are some of the most important aspects
of intelligence tradecraft."
The former NSA director claims that when it comes to metadata,
"no content of any kind is collected."
However, it has been proven over and over that metadata is how the
NSA can listen in on real-time conversations; attach geo-location to
calls and syphoning as much data as they want while storing it for
years.
Recently
a study from Stanford University (SU) Law School Center for Internet
and Society (LSCIS) shows exactly why metadata is an important topic
when it comes to surveillance and the National Security Agency (NSA).
Findings of the study showed that metadata is sensitive information
that can be analyzed to reveal intimate and personal details about the
person being spied on.
During the project initiated by Stanford Security Lab (SSL),
requested that the 500 volunteers install the ‘MetaPhone’ app to their
mobile devices.
The participants, who
used Facebook to install the app, allowed
researchers to syphon information from their smartphone at will,
including:
-
Monitor phone calls
-
Record text messages
-
Geo-location
-
Duration of call
In fact, when hacking into a call, a trunk identifier can be used to
not only gather information about the call, but to listen in on the
conversation from both the caller and receiver.
Trunking is the way that the police can change their signal when on
the radio every few seconds so that it cannot be syphoned by hackers. It
is used by cell phone towers to encrypt the signal for a secure line.
Trunking follows the sender and receiver when they change channels so
that GPS-like surveillance is conducted.
This allows the surveillance apparatus to have a continues stream
regardless of when the channel changes every few seconds, which in turn
allow those listening in to have a steady signal without breaks.
Effectively, they can listen to the entire conversation and follow the
signal as it changes.
The Future of Surveillance
...in
a Post-Snowden World
by Michael V. Hayden
Former director of the NSA and
the CIA
March 18, 2014
from
HuffingtonPost Website

Michael V. Hayden,
former director of the National Security Agency and
the Central Intelligence Agency.
The following comments
are adapted from his talk at the George Mason
University's School of Public Policy on Feb. 28 for
the National Security and Foreign Policy Lecture
Series.
A retired U.S. Air Force
four-star general, Hayden is also a distinguished
visiting professor at George Mason. Hayden provided
a very thought provoking discussion on "The Future
of Surveillance in a Post-Snowden World."
This article is prepared by General Hayden in
consultation with Patrick Mendis and Joey Wang.
THE SNOWDEN EFFECT
Edward Snowden has accelerated a
necessary and inevitable debate in American society regarding
surveillance.
In the course of doing so, however, I
believe that Snowden has badly shaped this debate and, in the course
of this acceleration, created a media frenzy that is largely focused
on headline-grabbing sensationalism rather than speaking to the hard
facts.
If the information compromised by former CIA officer Aldrich Ames
and that of the former FBI agent Robert Hanssen can be compared to
pails and possibly barrels, Snowden has ripped out the entire
plumbing because in the course of conducting his espionage, Snowden
has revealed far more than sensitive intelligence.
He has revealed sources and methods,
that is, the methodology by which the U.S. conducts its electronic
eavesdropping.
As a consequence, Snowden has
compromised an entire generation of investments in U.S. tactics,
techniques, and procedures. He represents the single greatest
hemorrhaging of 'legitimate' American secrets in the history of the
Republic.
Snowden has added a significant amount of drama to the debate.
Indeed, whatever beliefs he may have had as the defender of privacy,
his assertions and revelations have been inconsistent with his
overall effort. Well over 90 percent of what Snowden has revealed
has had nothing to do with Americans' communications.
Rather, Snowden has compromised how the
U.S. goes about collecting the communications of non-U.S. persons
who are, in fact, legitimate intelligence targets; these are some of
the most important aspects of intelligence tradecraft.
At the intersection of these revelations and the media frenzy it has
created; the "Snowden effect" has been press coverage that is far
less "reportorial" than "prosecutorial," in which a great number of
articles are written in an accusatory tone.
Let me dispel some myths spun by Snowden and the media coverage of
him:
For example, Section 215 of the USA Patriot Act is only concerned
with the collection of telephone metadata.
No content of any
communication is collected. Contrary to popular belief, it does not
mean that your entire life is in the possession of the National
Security Agency.
According to Title VII, Section 702 of the Foreign Intelligence
Surveillance Act, the NSA could obtain approval and access to email
accounts only through a generalized court order citing someone as
either a "terrorist, or proliferator, or a cyber-threat".
However, contrary to popular belief, at
no time did NSA ever have the authority to "free range" within mail
servers such as
Google, Yahoo, or
Microsoft.
Understanding such details matter.
So much of the debate provoked by
Snowden's actions has been conducted as if by competing bumper
stickers.
FUTURE THREATS
During the Cold War, I never lost any
sleep worrying about some religious fanatic living in a cave in the
Hindu Kush.
The industrial age trended to strengthen
the power of the state, and the ability to perpetrate violence on a
massive scale was centralized with the state.
In those days,
electronic surveillance was carried out against state actors such as
the Soviets and their strategic rocket forces. No civil libertarian
ever cared about those communications on a limited, state controlled
network.
The post-industrial age, however, has decentralized and pushed this
power downward to the individual, enabling those who intend to do
both good and evil. As a consequence, our personal communications
are now coming with legitimate foreign intelligence targets.
There is simply no way around it, and no
way to separate it.
There is also the question of the volume of modern communications.
In order to find the emerging threats in this ocean of data, the NSA
has had to resort to bulk collection as the only way data can be
analyzed for patterns of emerging threats and legitimate foreign
intelligence targets can be identified and isolated for intense
collection.
In the end, neither the NSA nor the CIA wants to do things that are
not consistent with the consensus view of American values. Our
intelligence agencies must, and will, accept any delimitation
defined by the American citizenry.
Tell me where the lines are. Just give me that political and legal
guidance, and we'll go play hardball. We'll stay inside the box.
At the same time, we will have to say,
"this will make you a little more
'comfortable', and it's going to make you a little less 'safe'."
We get it, but let's shake hands on that
last part - "a little less 'safe'."