|
by Christopher Ketcham
This article is from the May/June issue of
Radar Magazine from RadarOnLine Website
The federal government has been developing a highly classified plan that will override the Constitution in the event of a major terrorist attack
(Photo: Illustration by Brett Ryder) In the spring of 2007, a retired senior official in the U.S. Justice Department sat before Congress and told a story so odd and ominous, it could have sprung from the pages of a pulp political thriller. It was about a principled bureaucrat struggling to protect his country from a highly classified program with sinister implications.
Rife with high drama, it
included a car chase through the streets of Washington, D.C., and a tense
meeting at the White House, where the president's henchmen made the
bureaucrat so nervous that he demanded a neutral witness be present.
Comey had been a loyal political foot soldier of the Republican Party for many years. Yet in his testimony before the Senate Judiciary Committee, he described how he had grown increasingly uneasy reviewing the Bush administration's various domestic surveillance and spying programs.
Much of his testimony centered on an operation so clandestine he wasn't allowed to name it or even describe what it did. He did say, however, that he and Ashcroft had discussed the program in March 2004, trying to decide whether it was legal under federal statutes. Shortly before the certification deadline, Ashcroft fell ill with pancreatitis, making Comey acting attorney general, and Comey opted not to certify the program.
When he communicated his decision to the White House, Bush's men told him, in so many words, to take his concerns and stuff them in an undisclosed location.
Apparently, at the behest of President Bush himself, the White House tried, in Comey's words, "to take advantage of a very sick man," sending Chief of Staff Andrew Card and then-White House counsel Alberto Gonzales on a mission to Ashcroft's sickroom to persuade the heavily doped attorney general to override his deputy.
Apprised of their mission, Comey,
accompanied by a full security detail, jumped in his car, raced through the
streets of the capital, lights blazing, and "literally ran" up the hospital
stairs to beat them there.
Gonzales and Card were furious, departing without even acknowledging Comey's presence in the room. The following day, the classified domestic spying program that Comey found so disturbing went forward at the demand of the White House - "without a signature from the Department of Justice attesting as to its legality," he testified.
What was the mysterious program that had so alarmed Comey?
Political blogs buzzed for weeks with speculation. Though Comey testified that the program was subsequently readjusted to satisfy his concerns, one can't help wondering whether the unspecified alteration would satisfy constitutional experts, or even average citizens. Faced with push-back from his bosses at the White House, did he simply relent and accept a token concession?
Two months after Comey's testimony to Congress, the New York Times reported a tantalizing detail: The program that prompted him,
The larger mystery remained intact, however.
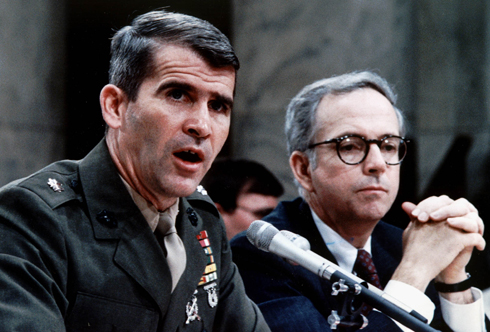
ONE NATION, UNDER SURVEILLANCE James Comey testifies before the Senate Judiciary Committee (Photo: Getty Images)
Addressing the nation from the Oval Office in 2005 after the first
disclosures of the NSA's warrantless electronic surveillance became public,
Bush insisted that the spying program in question was reviewed "every 45
days" as part of planning to assess threats to "the continuity of our
government."
In short, it's a road map for martial law.
Sources
familiar with the program say that the government's data gathering has been
overzealous and probably conducted in violation of federal law and the
protection from unreasonable search and seizure guaranteed by the Fourth
Amendment.
He and other sources tell Radar that the database is sometimes referred to by the code name Main Core.
One knowledgeable source claims that 8 million Americans are now listed in Main Core as potentially suspect. In the event of a national emergency, these people could be subject to everything from heightened surveillance and tracking to direct questioning and possibly even detention.
DESPERATE TIMES Should another 9/11 occur, Continuity of Governance plans developed during the Cold War go into effect (Photo: Getty Images)
According to one news report, even "national opposition to U.S.
military invasion abroad" could be a trigger.
Continuity of Governance plans that were developed during the Cold War and aggressively revised since 9/11 go into effect. Surviving government officials are shuttled to protected underground complexes carved into the hills of Maryland, Virginia, and Pennsylvania.
Power shifts to a "parallel government" that consists of scores of secretly preselected officials. (As far back as the 1980s, Donald Rumsfeld, then CEO of a pharmaceutical company, and Dick Cheney, then a congressman from Wyoming, were slated to step into key positions during a declared emergency.) The executive branch is the sole and absolute seat of authority, with Congress and the judiciary relegated to advisory roles at best.
The
country becomes, within a matter of hours, a police state.
The agency's incompetence in tackling natural
disasters is less surprising when one considers that, since its inception in
the 1970s, much of its focus has been on planning for the survival of the
federal government in the wake of a decapitating nuclear strike.
From the comfortable perspective of peaceful times, such behavior by the government may seem far-fetched. But it was not so very long ago that FDR ordered 120,000 Japanese Americans - everyone from infants to the elderly - be held in detention camps for the duration of World War II. This is widely regarded as a shameful moment in U.S. history, a lesson learned.
But a long trail of federal documents indicates that the possibility of large-scale detention has never quite been abandoned by federal authorities. Around the time of the 1968 race riots, for instance, a paper drawn up at the U.S. Army War College detailed plans for rounding up millions of "militants" and "American negroes," who were to be held at "assembly centers or relocation camps."
In the late 1980s, the Austin American-Statesman and other publications reported the existence of 10 detention camp sites on military facilities nationwide, where hundreds of thousands of people could be held in the event of domestic political upheaval.
More such facilities were commissioned in 2006, when Kellogg Brown & Root - then a subsidiary of Halliburton - was handed a $385 million contract to establish,
Just what those "new programs" might be is not specified.
(Photo: Getty Images)
Officials at the Department of Homeland Security begin actively scrutinizing people who - for a tremendously broad set of reasons - have been flagged in Main Core as potential domestic threats. Some of these individuals might receive a letter or a phone call, others a request to register with local authorities. Still others might hear a knock on the door and find police or armed soldiers outside.
In some instances, the authorities might just ask a few questions.
Other suspects might be arrested and escorted to federal holding facilities,
where they could be detained without counsel until the state of emergency is
no longer in effect.
But
when COG plans are shrouded in extreme secrecy, effectively unregulated by
Congress or the courts, and married to an overreaching surveillance state - as
seems to be the case with Main Core - even sober observers must weigh whether
the protections put in place by the federal government are becoming more
dangerous to America than any outside threat.
He has been told that the program utilizes software that makes predictive judgments of targets' behavior and tracks their circle of associations with "social network analysis" and artificial intelligence modeling tools.
An intelligence expert who has been briefed by high-level contacts in the Department of Homeland Security confirms that a database of this sort exists, but adds that,
CROWD CONTROL New Yorkers walk home on the afternoon of the September 11 attacks
(Photo: Getty Images)
A host of publicly disclosed programs, sources say, now supply data to
Main
Core. Most notable are the NSA domestic surveillance programs, initiated in
the wake of 9/11, typically referred to in press reports as "warrantless
wiretapping."
Authorities employ "sophisticated software programs" to sift through the data, searching for "suspicious patterns." In effect, the program is a mass catalog of the private lives of Americans.
And it's notable that the article hints at the possibility of programs like Main Core.
All of this information is archived on government supercomputers and,
according to sources, also fed into the Main Core database.
Additional information comes from a database known as the Terrorist Identities Datamart Environment, which generates watch lists from the Office of the Director of National Intelligence for use by airlines, law enforcement, and border posts.
According to the Washington Post, the Terrorist Identities list has quadrupled in size between 2003 and 2007 to include about 435,000 names. The FBI's Terrorist Screening Center border crossing list, which listed 755,000 persons as of fall 2007, grows by 200,000 names a year.
A former NSA officer tells Radar that the Treasury Department's Financial Crimes Enforcement Network, using an electronic-funds transfer surveillance program, also contributes data to Main Core, as does a Pentagon program that was created in 2002 to monitor antiwar protesters and environmental activists such as Greenpeace.
HERE'S LOOKING AT YOU From your late-night e-mails and travel plans to phone records and financial transactions, the government finds you fascinating - and may consider you a potential enemy of the state (Photo: Illustration by Brett Ryder)
Though not specifically familiar with the name Main Core, he adds,
A source regularly briefed by people inside the intelligence community adds:
If Main Core does exist, says Philip Giraldi, a former CIA counterterrorism officer and an outspoken critic of the agency, the Department of Homeland Security (DHS) is its likely home.
Giraldi notes that DHS already maintains a central list of suspected terrorists and has been freely adding people who pose no reasonable threat to domestic security.
UNDER REAGAN In the 1980s, control of the FBI's "security index" was reportedly transferred to none other than FEMA
(Photo: Getty Images) Would Main Core in fact be legal?
According to constitutional scholar Bruce Fein, who served as associate deputy attorney general under Ronald Reagan, the question of legality is murky:
Fein adds that it is virtually impossible to contest the legality of these kinds of data collection and spy programs in court,
But even if we never face a national emergency, the mere existence of the database is a matter of concern.
In any case, mass watch lists of domestic citizens may do nothing to make us safer from terrorism. Jeff Jonas, chief scientist at IBM, a world-renowned expert in data mining, contends that such efforts won't prevent terrorist conspiracies.
The overzealous compilation of a domestic watch list is not unique in postwar American history. In 1950, the FBI, under the notoriously paranoid J. Edgar Hoover, began to "accumulate the names, identities, and activities" of suspect American citizens in a rapidly expanding "security index," according to declassified documents.
In a letter to the Truman White House, Hoover stated that in the event of certain emergency situations, suspect individuals would be held in detention camps overseen by "the National Military Establishment."
By 1960, a congressional investigation later revealed, the FBI list of suspicious persons included,
This same FBI "security index" was
allegedly maintained and updated into the 1980s, when it was reportedly
transferred to the control of none other than FEMA (though the FBI denied
this at the time).
Tunney, the son of heavyweight boxing champion Gene Tunney and the inspiration for Robert Redford's character in the film The Candidate, found that the agency maintained electronic dossiers on at least 100,000 Americans that contained information gleaned from wide-ranging computerized surveillance. The database was located in the agency's secret underground city at Mount Weather, near the town of Bluemont, Virginia.
The senator's findings were confirmed in a 1976 investigation by the Progressive magazine, which found that the Mount Weather computers,
According to the Progressive, Mount Weather's databases were run,
JUST IN CASE The Miami Herald contended that Reagan loyalist Oliver North had spearheaded the development of a "secret contingency plan" (Photo: Getty Images)
A report in the Miami Herald contended that Reagan loyalist and Iran-Contra conspirator Colonel Oliver North had spearheaded the development of a,
The North plan also reportedly called for the detention of upwards of
400,000 illegal aliens and an undisclosed number of American citizens in at
least 10 military facilities maintained as potential holding camps.
Senator Daniel Inouye, chairman of the Senate Select Committee on Iran, immediately cut off his colleague, saying,
Though Brooks pushed for an answer, the line
of questioning was not allowed to proceed.
PROMIS, which has a strange and controversial history, was designed to track individuals - prisoners, for example - by pulling together information from disparate databases into a single record.
According to Wired,
Sources have suggested to Radar that government databases tracking Americans
today, including Main Core, could still have PROMIS-based legacy code from
the days when North was running his programs.
What is not yet clear is what sort of still-undisclosed programs may have been authorized by the Bush White House. Marty Lederman, a high-level official at the Department of Justice under Clinton, writing on a law blog last year, wondered,
Congress has tried, and mostly failed, to find out.
HISTORY'S LESSONS
Japanese Americans moved to internment camps in World War
II In July 2007 and again last August, Representative Peter DeFazio, a Democrat from Oregon and a senior member of the House Homeland Security Committee, sought access to the "classified annexes" of the Bush administration's Continuity of Government program.
DeFazio's interest was prompted by Homeland Security Presidential Directive 20 (also known as NSPD-51), issued in May 2007, which reserves for the executive branch the sole authority to decide what constitutes a national emergency and to determine when the emergency is over.
DeFazio found this unnerving.
In a press release issued last August, DeFazio went public with his concerns that the NSPD-51 Continuity of Government plans are,
Around the same time, he told the Oregonian:
The Military Commissions Act of 2006 effectively suspended habeas corpus and freed up the executive branch to designate any American citizen an "enemy combatant" forfeiting all privileges accorded under the Bill of Rights.
The John Warner National Defense Authorization Act, also passed in 2006, included a last-minute rider titled,
More troubling, in 2002, Congress authorized funding for the U.S. Northern Command, or NORTHCOM, which, according to Washington Post military intelligence expert William Arkin,
CREDIBLE WITNESS James Comey (Photo: Getty Images)
As of this writing, DeFazio, Thompson, and the other 433 members of the House are debating the so-called Protect America Act, after a similar bill passed in the Senate.
Despite its name, the act offers no protection for U.S. citizens; instead, it would immunize from litigation U.S. telecom giants for colluding with the government in the surveillance of Americans to feed the hungry maw of databases like Main Core.
The Protect America Act would legalize programs that appear to be unconstitutional. Meanwhile, the mystery of James Comey's testimony has disappeared in the morass of election year coverage.
None of the leading presidential candidates have been asked the questions that are so profoundly pertinent to the future of the country:
(Radar put these questions to spokespeople for the
McCain, Obama,
and Clinton campaigns, but at press time had yet to receive any responses.)
UPDATE
Since this article went to press, several documents have emerged to suggest the story has longer legs than we thought.
Most troubling among these is an October 2001 Justice Department memo that detailed the extra-constitutional powers the U.S. military might invoke during domestic operations following a terrorist attack.
In the memo, John Yoo, then deputy assistant attorney general,
(Yoo, as most readers know, is author of the infamous Torture Memo that, in bizarre fashion, rejiggers the definition of "legal" torture to allow pretty much anything short of murder.)
In the October 2001 memo, Yoo refers to a classified DOJ document titled "Authority for Use of Military Force to Combat Terrorist Activities Within the United States."
According to the Associated Press,
Attorney General John Mukasey last
month refused to clarify before Congress whether the Yoo memo was still in
force.
Penny Dodge, DeFazio's chief of staff, says otherwise.
|