|
mull leaning hard for access to
your info.
...will discuss next
month plans to force tech companies to break encryption on their
products.
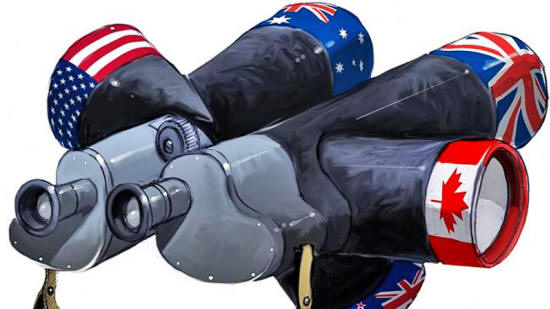
They will meet in Canada
with a focus on how to prevent "terrorists and organized criminals"
from "operating with impunity ungoverned digital spaces online,"
according to Australian prime minister Malcolm Turnbull.
Turnbull's comments reflect a more vague but similar response from UK prime minister Theresa May earlier this week in which she said she was focused on,
And the UK authorities have already put in a legislative placeholder for breaking encryption into Britain's Investigatory Powers Act.
Australia's administration is rather enamored with that new UK law, and hopes to implement it Down Under.
The United States meanwhile has been having a long debate on the issue of encryption, with tech firms battling it out with law enforcement in both public and private.
It is in the United States where the issue will ultimately be decided however, since the most widely used encrypted services, ranging from, ...are developed and run by US companies.
Not so much
Even the UK's heavily criticized anti-encryption law recognizes that it may be powerless to enforce encryption breaking on products and services that come from overseas - and online that geographic boundary doesn't exist.
The Five Eyes group is also going to have to decide how to deal with the mathematical realities of encryption.
If companies are forced to insert a backdoor into their encryption products in order to make their contents accessible, there is nothing to stop a malicious third party from doing the same: you cannot wall off a vulnerability.
Security experts have called the argument put forward by law enforcement and politicians - that they want access but don't want the bad guys to be able to do the same - "magical thinking."
The Five Eyes group needs to reach a decision on how to answer the inherent conundrum of magical thinking. Europe, which has been making its own noises about anti-encryption legislation, needs to do the same.
It is also possible of course that the vast and massively powerful spying machinery owned and run by the Five Eyes could be focused on cracking encryption.
To isolate specific messages of concern and then throw all computing resources at them.
Focus
Or, a third way could be for the security services from the five nations to oblige tech companies to develop a way to undermine specific devices - i.e., create a piece of software that could be sent to an individual's phone that would allow spies direct access to the device and so enable them to bypass encryption protection.
America's National Security Agency (NSA) is already known to have developed software that uses undiscovered vulnerabilities in software to give itself access to people's phones.
If you have full access to someone's phone (or other device), all the encryption in the world won't make a difference.
Although some tech companies have been public in their determination not to introduce backdoors, such as,
...it is notable that others have been silent or have called for compromise.
Google, for example, has stayed out of the fray, while Microsoft has repeatedly implied it is open to a shared solution.
Where exactly the decision comes down will be hard to say - not least because the security services will want the details to be as secret as possible.
Next month in Canada, they will likely emerge with a plan.
|